Auditing a Virtual Infrastructure: What they ask for
Posted: November 2, 2012 Filed under: Site Surveys, VMware | Tags: audit, esxi audit, it audit, security audit, vi audit, virtual environment audit, virtual infrastructure audit, vmware audit 2 CommentsGood day my friends! Good day it is, indeed! What makes it a good day, you ask? Well, for one, I’m being audited for the first time in my life. No, this isn’t an IRS audit (although I’m sure that would be more pleasant for me). This is an audit of my virtual  infrastructure. I assume people, for some odd reason, like to know their money is entrusted to competent folks (see, I work for a bank) that will safeguard it from the evils of the Internets, like this guy à
infrastructure. I assume people, for some odd reason, like to know their money is entrusted to competent folks (see, I work for a bank) that will safeguard it from the evils of the Internets, like this guy à
So we hired a company to do an internal audit of our business systems before the government does the real audit. This will give us a chance to make any necessary changes to the environment before anything’s found that could really affect us. My particular piece is, of course, the virtual infrastructure. Looking through the items requested, I like what I see. They’re basically looking at the security configuration: making sure only those that should have rights to vCenter or the ESXi hosts do, ensuring no one but trusted people have access to digital certificates, looking at the syslog config, looking at the ESXi firewall, and looking at the security posture of virtual machines. So here’s the list of what they’re asking for with a few sterilized examples. What are your experiences with Virtual Infrastructure audits?
-
Provide output of the command cat /etc/vmsyslog.conf | more
-
Provide output of the command esxcli network firewall ruleset list
-
Provide output of the command cat/etc/vmware/hostd/proxy.xml | more
-
Provide the screenshot of the SSL settings from vCenter (below)

-
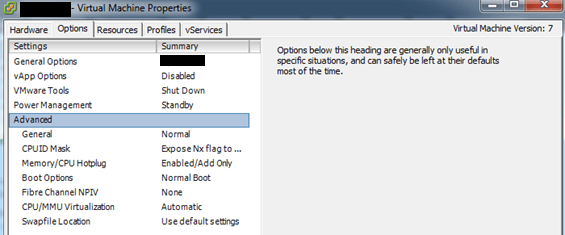
Provide a screenshot of the Configuration Parameters dialog box for a VM (we’re not exactly clear what or how much they want of this particular request, perhaps something like the below screenshot)
-
Provide a screenshot showing the member of the local Administrators group on the vCenter Server host (Windows)
-
Provide a screenshot of the accounts having Administrator privilege (global vCenter administrator) of vCenter Server

-
Provide a screen shot of the Windows file security permission of the SSL folder on the vCenter Server (C:\Documents and Settings\All Users\Application Data\VMware\VMware VirtualCenter\)
-
Provide a copy of the /etc/security, /etc/passwd, /etc/pam.d/passwd and /etc/group files
-
Provide a list of the VMware ESX/ESXi groups and permissions to the ESX/ESXi servers or vCenter.
-
Provide a copy of the output of the authentication mechanisms that are allowed on the ESX/ESXi servers. For each authentication mechanism, give the list of users. This is typically obtained by executing the following commands:
-
Kerberos – Typically obtained by executing the klist command. NOTE: This application will not be installed if Kerberos support is not enabled
-
LDAP – Typically obtained by executing /usr/bin/getent –service=LDAP passwd
-
NIS – Typically obtained by executing /usr/bin/ypcat or /usr/bin/getent –service=NIS passwd
-
Local – Typically obtained by executing cat /etc/passwd
-
-
Provide a list of users/groups and permissions to the ESX/ESXi servers or vCenter.





No questions about SSO? Audit company already living in the past.
Great auditing a virtual infrastructure.